You won’t want a quantum laptop of your personal to use quantum computing inside the destiny soundly. For the first time, researchers have proven that even normal classical PC users should remotely get entry to quantum computing resources online while maintaining their quantum computations securely hidden from the quantum computer itself.
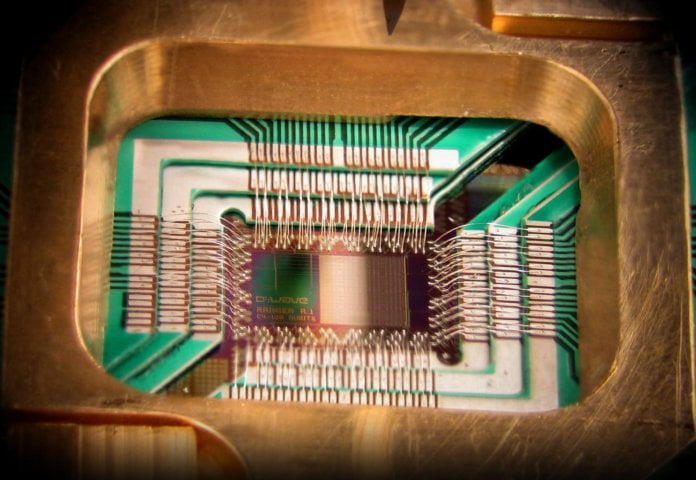
Tech giants, including Google and IBM, are racing to build well-known quantum computers that would someday examine tens of millions of feasible solutions faster than nowadays’s most powerful classical supercomputers. Such groups have also begun providing online admission to their early quantum processors as a glimpse of how everybody may want to faucet the electricity of cloud-primarily based quantum computing.
Until lately, most researchers believed there had been no manner for far-flung customers to soundly disguise their quantum computations from prying eyes unless they also possessed quantum computer systems. That assumption is now being challenged using researchers in Singapore and Australia via a new paper published in the eleven July problem of the journal Physical Review X journal.
“Frankly, I think we’re all quite surprised that that is possible,” says Joseph Fitzsimons, a theoretical physicist for the Centre for Quantum Technologies at the National University of Singapore and most important investigator at the look. “Some outcomes showed that it was not going to a classical person as a way to disguise [delegated quantum computations] flawlessly, and I think many of us in the area had interpreted this as evidence that nothing beneficial can be hidden.”
The approach for supporting classical laptop customers to cover their quantum computations relies upon a method called measurement-based quantum computing. Quantum computing’s predominant promise is predicated upon leveraging quantum bits (qubits) of data that may exist concurrently as each 1s and 0s—unlike classical computing bits that exist as 1 and 0. That means qubits can simultaneously represent and process many extra states of information than classical computing bits.
READ MORE :
In size-based quantum computing, a quantum laptop places all its qubits into a particular nation of quantum entanglement so that any adjustments to an unmarried qubit affect all of the qubits. Next, qubits are, in my opinion, measured one at a time in a sure order that specifies the program being run on the quantum computer. A remote user can offer step-by-step instructions for each qubit’s size that encodes each entry information, and this system is run. Crucially, each measurement relies upon the final results of preceding measurements.
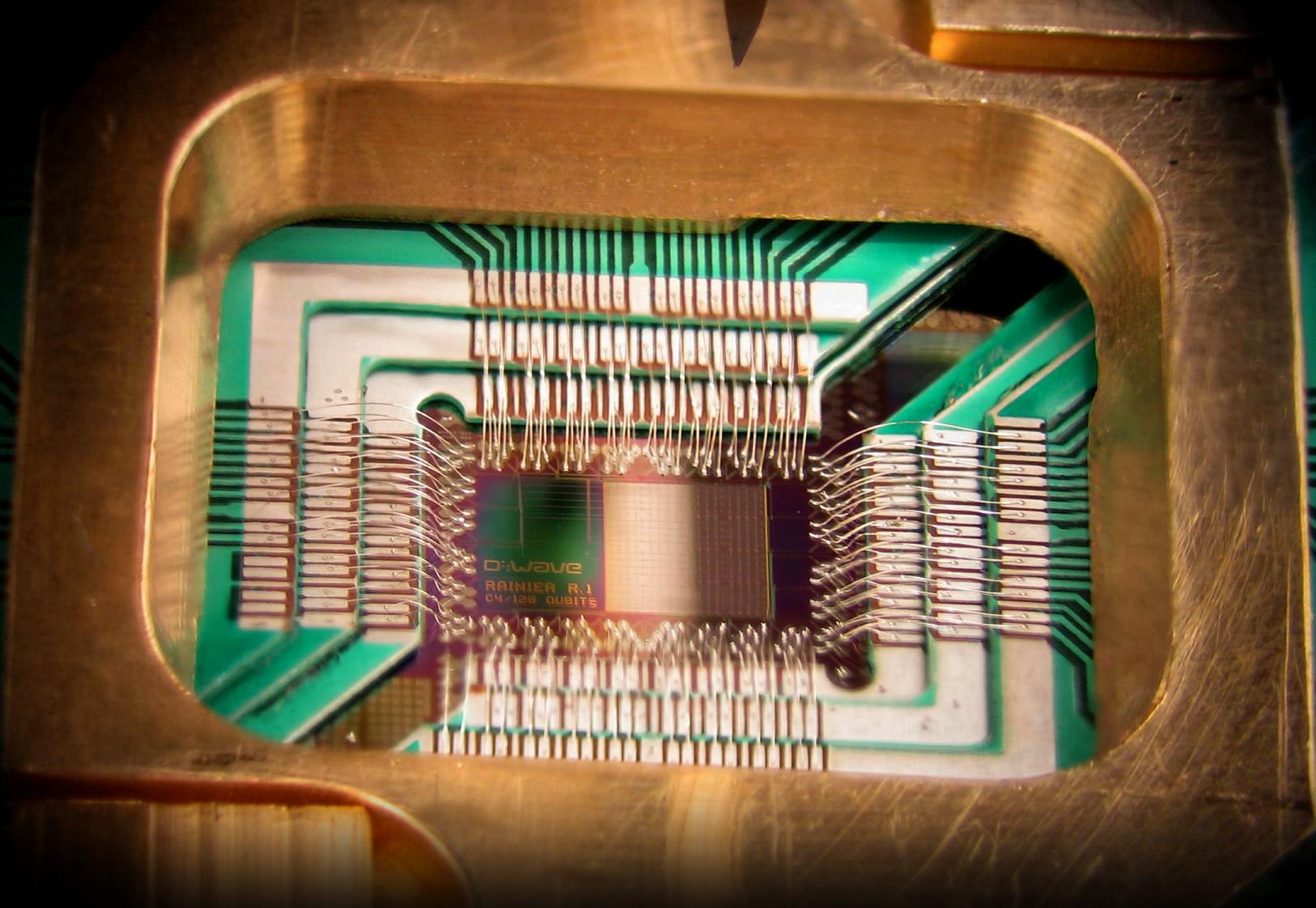
Fitzsimons and his colleagues discovered how to make the most of this step-wise approach to quantum computing and acquire a new form of “blind quantum computation” safety. They showed how remote users counting on classical computer systems could conceal the meaning behind each step of the dimension series from the quantum P.C. appearing in the computation. In that manner, the proprietor of the quantum P.C. can’t tell the position of each dimension step and which qubits were used for inputs, operations, or outputs.
The locating runs counter to preceding assumptions that it became impossible to guarantee data privacy for customers counting on ordinary classical computers to get the right of entry to quantum computers remotely. But Fitzsimons says that early comments to the institution’s paintings have been “very nice” because the proposed safety mechanism is defined as the “glide ambiguity effect”—in all fairness, truthful. He explains:
Previous effects showed that it became viable to flawlessly conceal computation if the user had some small quantum device to put together or degree quantum states. However, formerly, no development has been made in the case of a consumer without this sort of quantum capabilities, except they had to get entry to more than one quantum computer, which had been guaranteed not to communicate. We introduce a way that allows a classical person to hide computations from a quantum PC as simply as you may want if you can access a device over the Internet.
This first extensive step toward comfortable cloud quantum computing for all is part of a broader effort targeted at blind quantum computation spanning more than ten years for Fitzsimons. The studies team’s paintings became both at once and indirectly supported through funding from the U.S. Air Force Office of Scientific Research, the Australian Research Council,
the U.S. Defense Advanced Research Projects Agency (DARPA), and the Singapore National Research Foundation.
Several critical questions remain before this new technique of blind quantum computation can be positioned to paintings. Theoretically, state-of-the-art studies have only proven that a quantum laptop with no earlier information about quantum computation will not have “any reasonable possibility of fulfillment” in identifying the steps behind that computation. That no longer completely rules out the chance that the quantum computer can piece together such analyses if it has many facts about the calculation. Fitzsimons and his colleagues wish to look at this in their upcoming work.
Another fascinating query involves whether this method can help classical P.C. users verify the accuracy of quantum computations performed remotely on a quantum P.C. This ought to mean embedding “hidden test computations” in the foremost quantum computation to assist in locating “any deviation through a malicious or defective quantum laptop,” Fitzsimons says.
If this works, groups including Google and IBM could ultimately offer cloud quantum computing to guarantee data privacy and accuracy. “With some of the companies providing access to prototype quantum processors over the Internet,” Fitzsimons says, “It was a herbal query to ask whether it is probably viable for a user to hide computation, even earlier than quantum verbal exchange. Will become possible.”